Steganography
Blog Credit: Trupti Thakur
Image Courtesy: Google
Steganography
Steganography is the technique of hiding secret data within an ordinary, non-secret, file or message in order to avoid detection; the secret data is then extracted at its destination. The use of steganography can be combined with encryption as an extra step for hiding or protecting data.
Image Steganography
Steganography is derived from two Greek words:’stegos,’ which means ‘to cover,’ and ‘grayfia,’ which means ‘writing,’ thus translating to ‘covered writing,’ or ‘hidden writing.’ Steganography is a method of concealing sensitive information by embedding it in an audio, video, image, or text file. It is one of the techniques used to protect confidential or sensitive data from malicious attacks.
What distinguishes it from cryptography?
Cryptography and steganography are both methods for concealing or protecting sensitive information. They differ in that cryptography makes the data unreadable or conceals the meaning of the data, whereas steganography conceals the existence of the data.
Cryptography is analogous to writing a letter in a secret language: people can read it but won’t understand what it means. The existence of a (likely secret) message, on the other hand, would be obvious to anyone who sees the letter, and if someone knows or figures out your secret language, your message can be easily read.
If you used steganography in the same situation, you would conceal the letter inside a pair of socks that you would give to the intended recipient. To those who are unaware of the message, your gift appears to be nothing more than the socks. However, the intended recipient is aware of what to look for and discovers the message hidden within them.
Cryptography is frequently used to augment the security provided by steganography. Encryption algorithms are used to encrypt secret data before it is embedded in cover files.
Steganography can be used to conceal almost any type of digital content, including text, image, video or audio content; the data to be hidden can be hidden inside almost any other type of digital content. The content to be concealed through steganography — called hidden text — is often encrypted before being incorporated into the innocuous-seeming cover text file or data stream. If not encrypted, the hidden text is commonly processed in some way in order to increase the difficulty of detecting the secret content.
What are examples for steganography?
Steganography is practiced by those wishing to convey a secret message or code. While there are many legitimate uses for steganography, malware developers have also been found to use steganography to obscure the transmission of malicious code.
Forms of steganography have been used for centuries and include almost any technique for hiding a secret message in an otherwise harmless container. For example, using invisible ink to hide secret messages in otherwise inoffensive messages; hiding documents recorded on microdot — which can be as small as 1 millimeter in diameter — on or inside legitimate-seeming correspondence; and even by using multiplayer gaming environments to share information.
How is steganography used today?
In modern digital steganography, data is first encrypted or obfuscated in some other way and then inserted, using a special algorithm, into data that is part of a particular file format such as a JPEG image, audio or video file. The secret message can be embedded into ordinary data files in many different ways. One technique is to hide data in bits that represent the same color pixels repeated in a row in an image file. By applying the encrypted data to this redundant data in some inconspicuous way, the result will be an image file that appears identical to the original image but that has “noise” patterns of regular, unencrypted data.
The practice of adding a watermark — a trademark or other identifying data hidden in multimedia or other content files — is one common use of steganography. Watermarking is a technique often used by online publishers to identify the source of media files that have been found being shared without permission.
While there are many different uses of steganography, including embedding sensitive information into file types, one of the most common techniques is to embed a text file into an image file. When this is done, anyone viewing the image file should not be able to see a difference between the original image file and the encrypted file; this is accomplished by storing the message with less significant bites in the data file. This process can be completed manually or with the use of a steganography tool.
What are the advantages of steganography over cryptography?
Steganography is distinct from cryptography, but using both together can help improve the security of the protected information and prevent detection of the secret communication. If steganographically-hidden data is also encrypted, the data may still be safe from detection — though the channel will no longer be safe from detection. There are advantages to using steganography combined with encryption over encryption-only communication.
The primary advantage of using steganography to hide data over encryption is that it helps obscure the fact that there is sensitive data hidden in the file or other content carrying the hidden text. Whereas an encrypted file, message or network packet payload is clearly marked and identifiable as such, using steganographic techniques helps to obscure the presence of the secure channel.
Steganography software
Steganography software is used to perform a variety of functions in order to hide data, including encoding the data in order to prepare it to be hidden inside another file, keeping track of which bits of the cover text file contain hidden data, encrypting the data to be hidden and extracting hidden data by its intended recipient.
There are proprietary as well as open source and other free-to-use programs available for doing steganography. OpenStego is an open source steganography program; other programs can be characterized by the types of data that can be hidden as well as what types of files that data can be hidden inside. Some online steganography software tools include Xiao Steganography, used to hide secret files in BMP images or WAV files; Image Steganography, a Javascript tool that hides images inside other image files; and Crypture, a command line tool that is used to perform steganography.
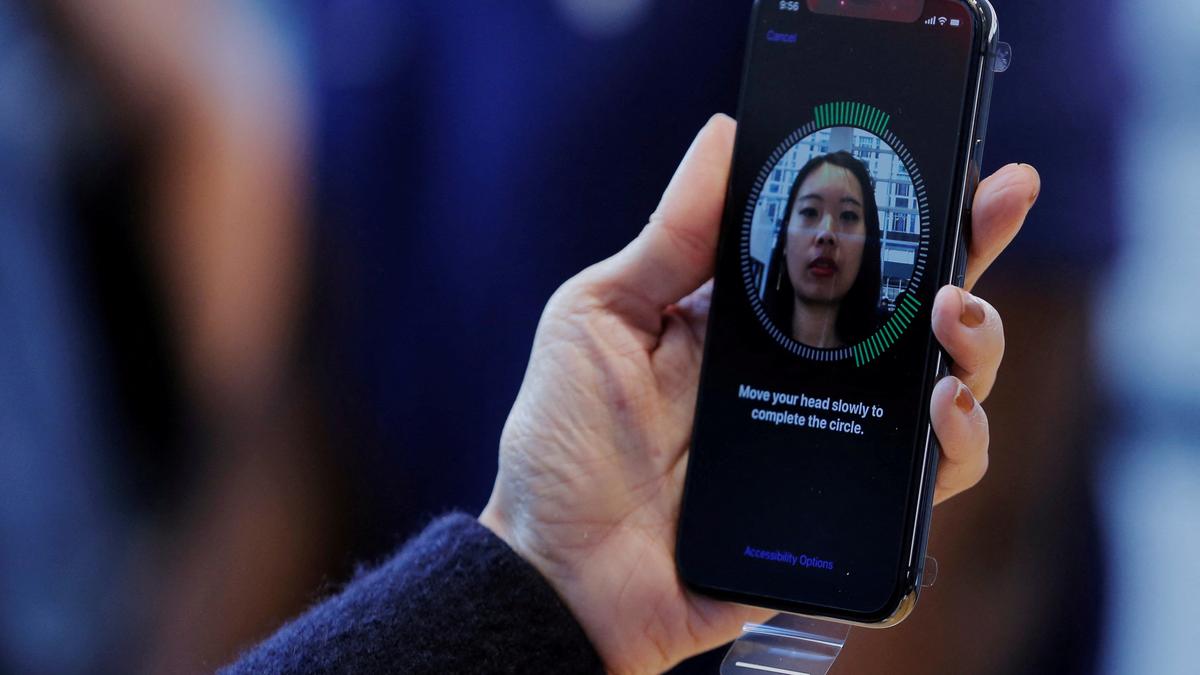
Image Steganography –
Image Steganography, as the name implies, is the process of concealing data within an image file. The image chosen for this purpose is referred to as the cover image, and the image obtained after steganography is referred to as the stego image.
How does it work?
In memory, an image is represented as a N*M (for greyscale images) or N*M*3 (for colour images) matrix, with each entry representing the intensity value of a pixel. Image steganography embeds a message into an image by changing the values of some pixels chosen by an encryption algorithm.
Is steganography a safe way to communicate?
When steganography is used alone, it provides security through obscurity, which may result in the secret message being revealed. Combining steganography and cryptography is the most effective way to hide a message from adversaries while still protecting it if it is discovered.
What algorithm is used in steganography?
His steganography method involves hiding a large amount of data (image, audio, and text) within a colour bitmap (bmp) image. In his study, the image will be filtered and segmented, with bits replacement applied to the appropriate pixels. These pixels are chosen at random rather than in any particular order.
The process of steganalysis is used to detect the message within the cover image. This can be accomplished by comparing the image to the cover image, plotting histograms, or detecting noise. While efforts are being made to develop new algorithms that are more resistant to such attacks, efforts are also being made to improve existing algorithms for steganalysis, which detects the exchange of secret information between terrorists or criminal elements.
Blog By: Trupti Thakur

24
JunSteganography
Jun 24, 2023Recent Blog
AI HallucinationsMay 16, 2025
India’s Steps Into 6GMay 15, 2025
The New Accessibility Feature of AppleMay 14, 2025
The Digital Threat Report 2024May 13, 2025
The MADMAX ExperimentMay 12, 2025