Blog By: Priyanka Rana
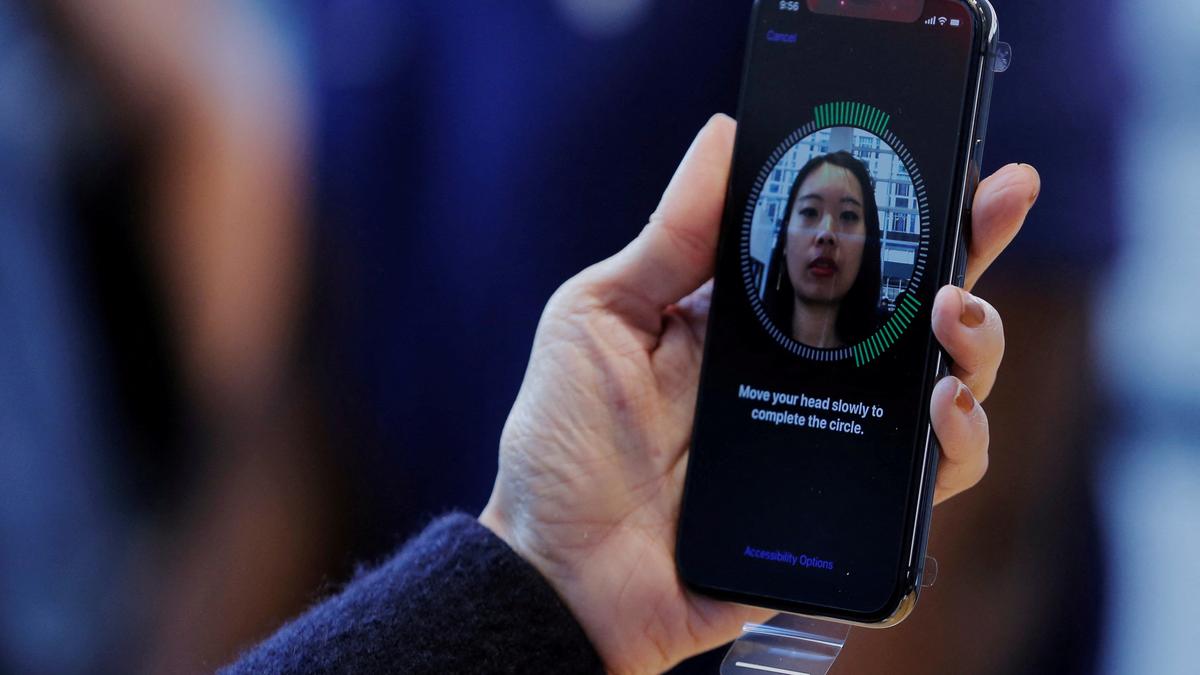
Spoofing Attack
Spoofing is the act of disguising a communication or identity so that it appears to be associated with a trusted, authorized source. Spoofing attacks can take many forms, from the common email spoofing attacks that are deployed in phishing campaigns to caller ID spoofing attacks that are often used to commit fraud.
The best way to prevent a spoofing attack, on the user education side of things, is to keep a lookout for signs that you are being spoofed. For example, a phishing attack that uses email spoofing may feature unusual grammar, poor spelling, or awkward language. The message contained may be urgent in nature, designed to provoke panic and telling you to take immediate action.You may also notice, upon further inspection, that the sender’s email address is off by one letter or that the URL featured within the message has a slightly different spelling than it should. A best-in-class incident detection and response solution can protect your organization even further by proactively notifying you in the event that anomalous user activity is detected.
Fake job offers, fake banking-related messages, fake lottery messages, money refund scams, and password reset messages are some examples of Text Message Spoofing. Spoofed messages are difficult to identify until the person is aware of where to look for them. The sender’s name cannot be clicked and replied.
Stay safe from frauds

04
NovSpoofing Attack
Nov 04, 2023Recent Blog
India’s Steps Into 6GMay 15, 2025
The New Accessibility Feature of AppleMay 14, 2025
The Digital Threat Report 2024May 13, 2025
The MADMAX ExperimentMay 12, 2025
The EntraID Data ProtectionMay 10, 2025