Top 5 Practices of Protecting Data
- Mar 02, 2023
The protection of data is a crucial concern for individuals, businesses, and organizations of all sizes. With the increasing reliance on technology for storing and transmitting sensitive information, the threat of data breaches and theft has become a major issue. In 2022, there were more than 2000 publicly disclosed data breaches, with 60% being a result of […]
Momentum 2.0
- Mar 01, 2023
Momentum 2.0 Blog Credit: Trupti Thakur Image Courtesy: Google Delhi Metro Rail Corporation (DMRC) will soon launch India’s first virtual shopping app, ‘Momentum 2.0’ for the Delhi metro commuters, the officials said on Sunday. The passengers will be able to get customized services like last-mile connectivity options, e-shopping choices, and digital lockers at the metro stations via […]
ChatGPT and the Future of Cybersecurity
- Mar 01, 2023
ChatGPT isn’t without its own bugs. Users have flagged the answers the chatbot provides for errors on numerous occasions. And, of course, you should always thoroughly test any code the AI writes before use. Still, the machine continues to learn as it interacts with the world. By design, it will get better and better at […]
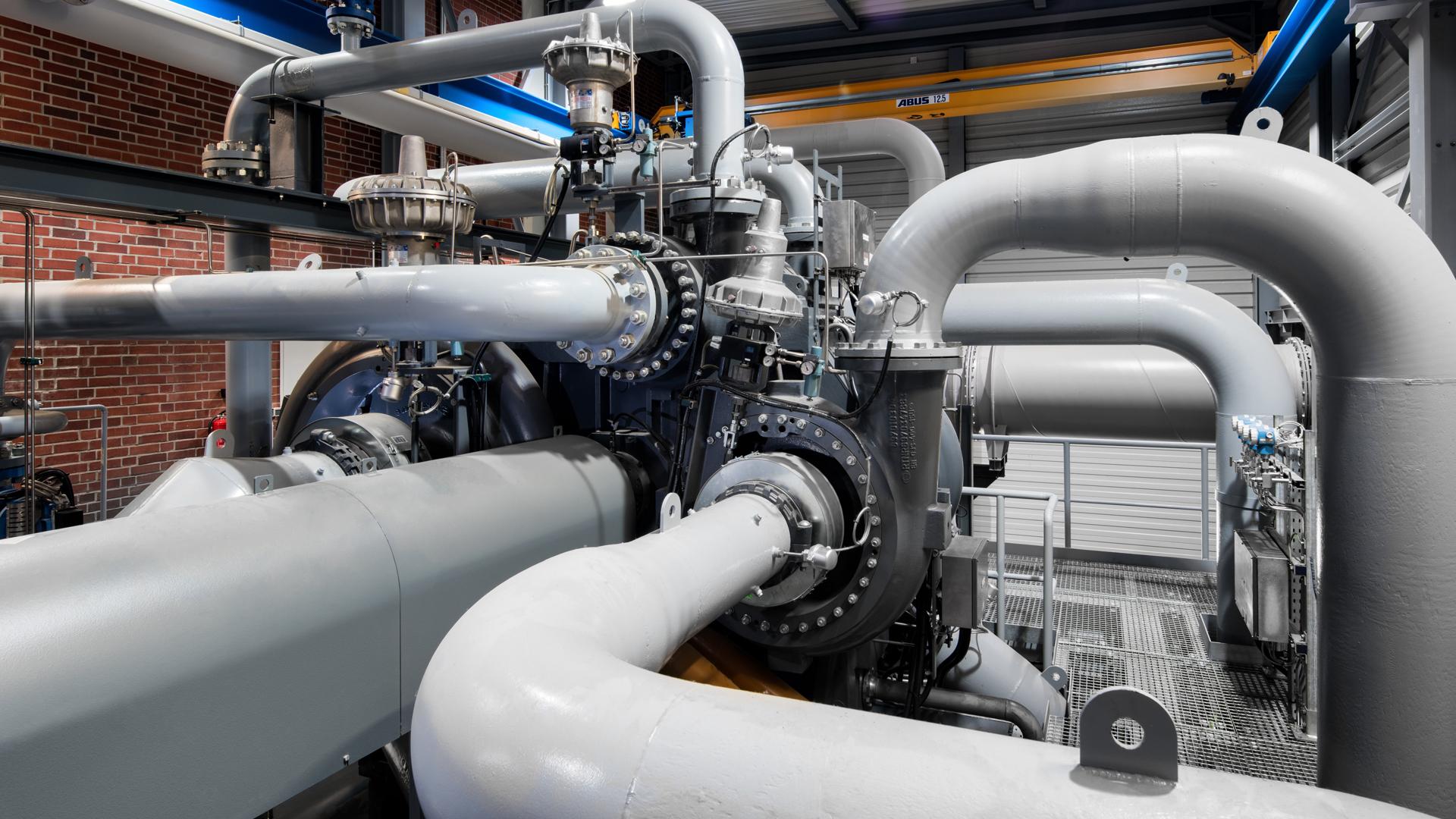
Compressed Air Based Transportation System By IIT Kanpur
- Feb 20, 2023
Compressed Air Based Transportation System Blog Credit: Trupti Thakur Image Courtesy: Google The Indian Institute of Technology (IIT) Kanpur has developed an energy-efficient compressed air-based pipeline system […]
PCI DSS
- Feb 18, 2023
What is PCI DSS The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards formed in 2004 by Visa, MasterCard, Discover Financial Services, JCB International and American Express. Governed by the Payment Card Industry Security Standards Council (PCI SSC), the compliance scheme aims to secure credit and debit card transactions against data […]
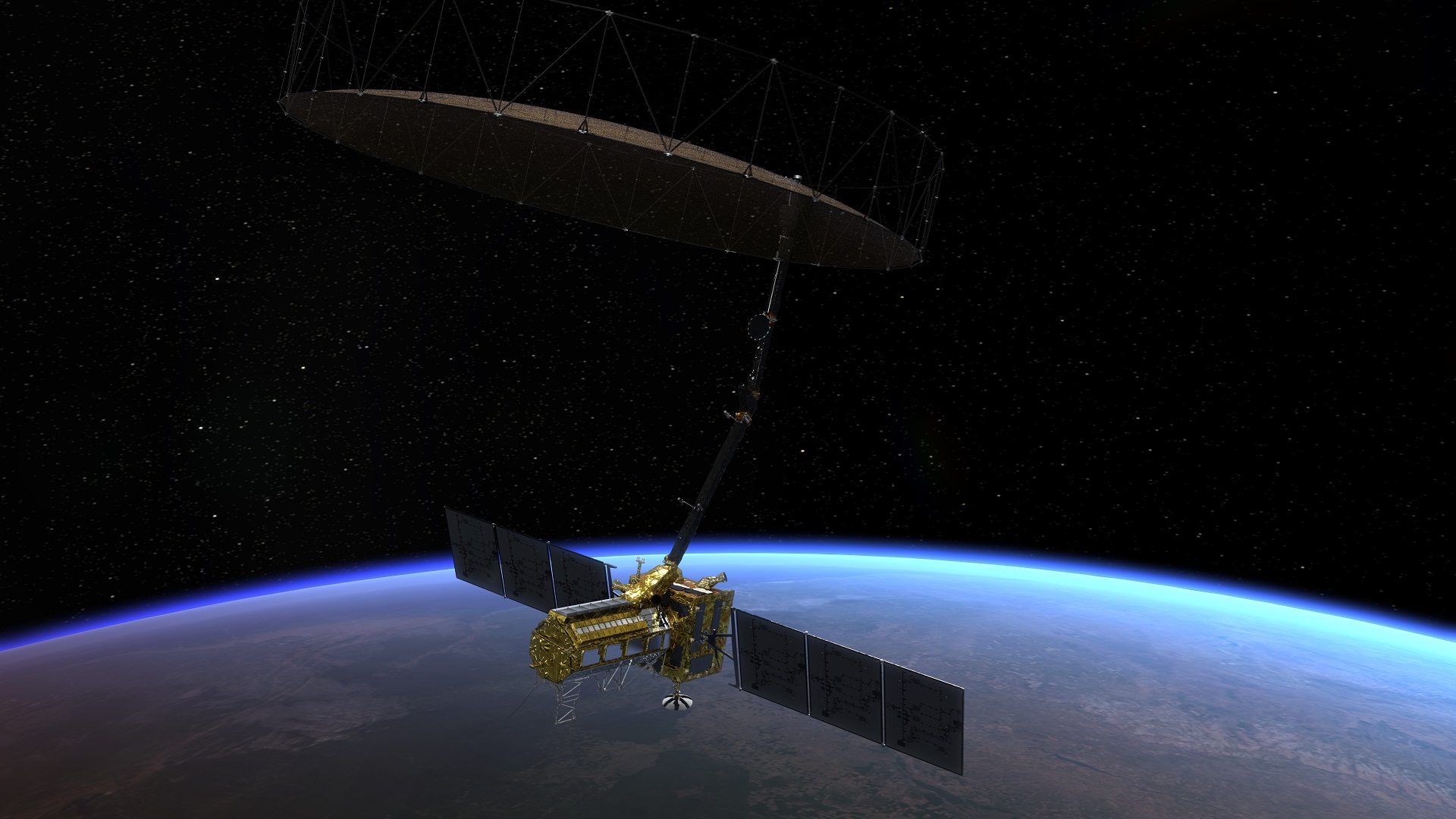
NISAR- NASA-ISRO Synthetic Aperture Radar Mission
- Feb 17, 2023
NASA-ISRO Synthetic Aperture Radar Mission Blog Credit: Trupti Thakur Image Courtesy: Google ABOUT NISAR The NASA-ISRO Synthetic Aperture Radar mission is a joint project between NASA and ISRO to co-develop and launch a dual-frequency synthetic aperture radar on an Earth observation satellite. The satellite will be the first radar imaging satellite to use dual frequencies. […]
Red Teaming
- Feb 14, 2023
Red teaming is a knowledge driven security assessment designed to completely test associations’ cyber resilience in addition to danger discovery and incident response capabilities. Red teaming is performed by ethical hackers, who reflect the states of a veritable cyber-attack by using similar tactics, techniques and procedure (TTPs) utilized by criminal foes. This guarantees that commitment […]
Cyber Attack And Its Types
- Feb 13, 2023
Types of Cyber Attacks There are many varieties of cyber attacks that happen in the world today. If we know the various types of cyberattacks, it becomes easier for us to protect our networks […]
Web Content Accessibility Guidelines- WCAG
- Feb 13, 2023
Web Content Accessibility Guidelines (WCAG) The Web Content Accessibility Guidelines (WCAG) are a significant resource for organizations, associations, and different elements who need to […]
Traffic Management System For Drones
- Feb 11, 2023
Traffic Management System for Drones Blog Credit: Trupti Thakur Image Courtesy: Google Touted as the world’s most cutting-edge unmanned traffic […]
Robotic Process Automation (RPA)
- Feb 10, 2023
Robotic Process Automation (RPA) Blog Credit : Trupti Thakur Image Courtesy: Google What is robotic process automation? Robotic process automation (RPA) is a software technology that makes it easy to build, deploy, and manage software robots that emulate humans’ actions interacting with digital systems and software. Just like people, software robots can do things like […]
Data Migration
- Feb 10, 2023
Data Migration What is data migration? In general terms, Data Migration is the transfer of […]